Everything about Sniper Africa
The 25-Second Trick For Sniper Africa
Table of ContentsThe 8-Minute Rule for Sniper AfricaThe smart Trick of Sniper Africa That Nobody is Talking AboutExcitement About Sniper AfricaA Biased View of Sniper AfricaExamine This Report on Sniper AfricaSome Known Incorrect Statements About Sniper Africa Sniper Africa Can Be Fun For Anyone
This can be a specific system, a network area, or a theory triggered by an announced susceptability or spot, info about a zero-day exploit, an anomaly within the safety and security information set, or a request from somewhere else in the organization. Once a trigger is identified, the searching efforts are concentrated on proactively searching for anomalies that either confirm or refute the theory.
The smart Trick of Sniper Africa That Nobody is Discussing
This process might include the use of automated devices and questions, together with hand-operated analysis and correlation of information. Unstructured searching, likewise known as exploratory searching, is an extra flexible strategy to hazard searching that does not rely upon predefined criteria or theories. Rather, risk hunters use their experience and instinct to search for possible hazards or vulnerabilities within an organization's network or systems, usually concentrating on locations that are viewed as risky or have a background of security cases.
In this situational technique, danger hunters use threat knowledge, along with other relevant information and contextual details about the entities on the network, to identify possible dangers or susceptabilities connected with the scenario. This might involve the use of both organized and unstructured searching strategies, in addition to cooperation with various other stakeholders within the organization, such as IT, lawful, or company groups.
Sniper Africa Fundamentals Explained
(https://linktr.ee/sn1perafrica)You can input and search on threat knowledge such as IoCs, IP addresses, hash values, and domain names. This process can be incorporated with your security info and occasion monitoring (SIEM) and hazard intelligence tools, which use the knowledge to hunt for hazards. Another excellent source of intelligence is the host or network artefacts offered by computer emergency situation reaction teams (CERTs) or information sharing and analysis centers (ISAC), which might enable you to export automated informs or share essential information concerning new strikes seen in various other companies.
The initial action is to determine APT teams and malware attacks by leveraging international detection playbooks. This strategy generally lines up with hazard frameworks such as the MITRE ATT&CKTM framework. Here are the activities that are usually associated with the procedure: Use IoAs and TTPs to determine threat actors. The hunter examines the domain name, environment, and assault behaviors to create a hypothesis that straightens with ATT&CK.
The goal is situating, determining, and after that isolating the danger to stop spread or proliferation. The hybrid risk hunting method integrates all of the above approaches, permitting security experts to tailor the hunt. It typically integrates industry-based searching with situational recognition, incorporated with defined searching needs. The search can be customized utilizing data concerning geopolitical concerns.
What Does Sniper Africa Do?
When operating in a safety and security operations center (SOC), hazard hunters report to the SOC manager. Some important skills for a great threat seeker are: It is crucial for risk seekers to be able to interact both vocally and in composing with great clarity regarding their activities, from examination all the method via to searchings for and suggestions for removal.
Information violations and cyberattacks cost companies numerous bucks annually. These pointers can help your company better identify these risks: Risk hunters need to look via anomalous tasks and recognize the reference actual threats, so it is crucial to comprehend what the regular functional tasks of the company are. To complete this, the threat hunting team works together with crucial employees both within and beyond IT to gather important details and insights.
Indicators on Sniper Africa You Need To Know
This process can be automated using a technology like UEBA, which can reveal regular operation conditions for an atmosphere, and the individuals and makers within it. Danger seekers utilize this technique, obtained from the armed forces, in cyber war. OODA stands for: Consistently collect logs from IT and safety systems. Cross-check the information versus existing details.
Identify the appropriate course of action according to the case condition. In instance of an attack, execute the event reaction strategy. Take steps to avoid comparable assaults in the future. A risk searching team must have enough of the following: a danger hunting group that includes, at minimum, one seasoned cyber danger seeker a standard risk searching framework that collects and organizes security events and occasions software application developed to determine anomalies and find assailants Hazard hunters make use of solutions and tools to locate suspicious activities.
Sniper Africa - An Overview

Unlike automated hazard detection systems, risk searching counts heavily on human instinct, matched by sophisticated tools. The risks are high: A successful cyberattack can bring about information violations, financial losses, and reputational damage. Threat-hunting tools supply safety and security groups with the understandings and abilities required to remain one action in advance of assaulters.
7 Easy Facts About Sniper Africa Shown
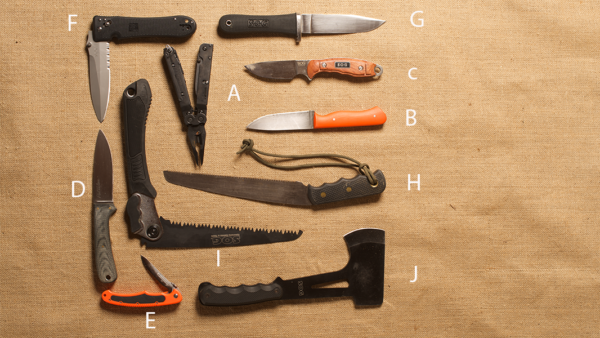
Here are the characteristics of reliable threat-hunting devices: Constant surveillance of network website traffic, endpoints, and logs. Smooth compatibility with existing safety and security infrastructure. hunting jacket.